Increased aviation capacity, cost savings and a continuously reducing CO2 impact build on reliable interoperability and information exchanged within and between various ANSPs and connected players. This impacts SMC and Cybersecurity requirements.
Today’s ATC interoperability and System-wide Information Management
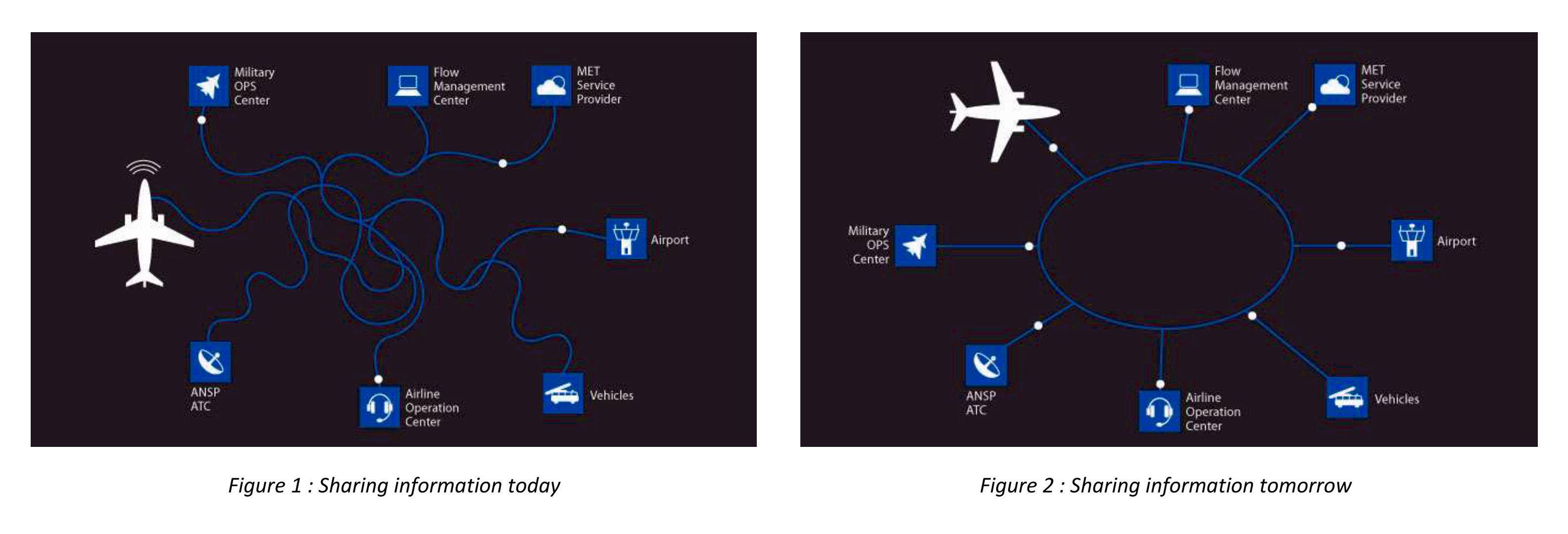
Figure 1 shows the current situation of interconnectedness for many ANSPs (there are probably more players involved in many ANSPs as displayed in the infographics).
Already today, there are data flows across enterprise boundaries. Major connected players are aircraft, ANSPs / ATC, airline operations centers, military OPS centers, flow management centers, meteorology service centers, airports, ground vehicles, and more.
The relative chaotic connections between the various players show that there is much scope for improvement which can be accomplished through the implementation of standardized and seamless interoperable data exchange.
SWIM is an ICAO initiative to provide exactly this. It is the emerging design concept for System-wide Information Management, initiated and mandated by ICAO as well as by the European Single European Sky Initiative. Its ATM Information Reference Model (AIRM) is currently piloted by the AIRM community in the context of EU Pilot Common Projects (PCP). In Pilots, SWIM proved to be more cost and time efficient with positive effects on the environment.
Source: SESARJU’s factsheet on SWIM
The implications on System Monitoring and Control (SMC)
EU Regulation 2017/373 requires from ANSPs to secure safe and uninterrupted Air Traffic through continuously monitored infrastructure, networks, but also data and communication.
Given the heterogeneous origin of data and the location of critical infrastructure outside of an ANSP’s governance area, monitoring of system health and data integrity is becoming an increasingly complex task.
Different governance areas means that monitoring and control requires different roles and authority. For instance an ATSEP should be able to monitor system health of a radar in a different governance area (e.g. a military radar or a radar placed in a neighboring Flight Information Region (FIR)). But he or she should probably not have control rights. In the own FIR, authority to monitor and control is normally also segmented based on the ATSEP’s job profile. Some rights, like switching important transceivers, might be restricted to higher ranked personnel, to avoid accidental or malicious system degradation.
Read more about System Monitoring and Control in our special series of SMC articles.
Cybersecurity
System interconnectedness, pan-regional monitoring and control and cybersecurity are closely related. Interconnected regions provide more and larger attack surfaces.
A well-thought process for computer security incident response is an increasingly important task in the ATSEP realm. ATSEPs need to be well qualified in this field in order to be continuously monitoring their infrastructure for malicious intrusion and compromise and to restore a safe state in due time in case of intrusion.
Remote monitoring and control access may adhere to the risk that an account may be taken over by a hacker remotely through this SMC pathway. Intelligently segmented and hierarchized authorization of monitoring and control personnel are mandatory. And ANSP’s cybersecurity policy and its SMC-policy should be closely intertwined.
Read more about System Monitoring and Control in our special series of articles on cybersecurity in Air Traffic Control.
Qualification
EU Regulation 2017/373 as well as diverse ICAO documents mandate ATSEP qualification on controlling and monitoring infrastructure, data and communication. They also explicitly require qualification on cybersecurity issues.
SkyRadar
SkyRadar provides a pedagogically enhanced System Monitoring and Control environment for ATSEP qualification including servers, networks and even a complete ATC/ATM system. The SMC system can come with a reference cybersecurity architecture and a process for computer security incident response.
Stay tuned to be always the first to learn about new use cases and solutions in SMC and cybersecurity qualification for ATSEPs.
Or simply talk to us to discuss your training solution.