Aviation and Air Traffic Control in particular risk to be a prominent target for hackers. There is no reason to panic, as there are solutions. But the technical teams, ATSEP in particular need to get active, now!
June and July 2021 were shocking for the interconnected world. Supposedly protected areas like the American gas pipelines, the Irish health system, Air India, and now central American cloud service providers were compromised by hackers, demanding (and partially getting) high amounts of ransom.
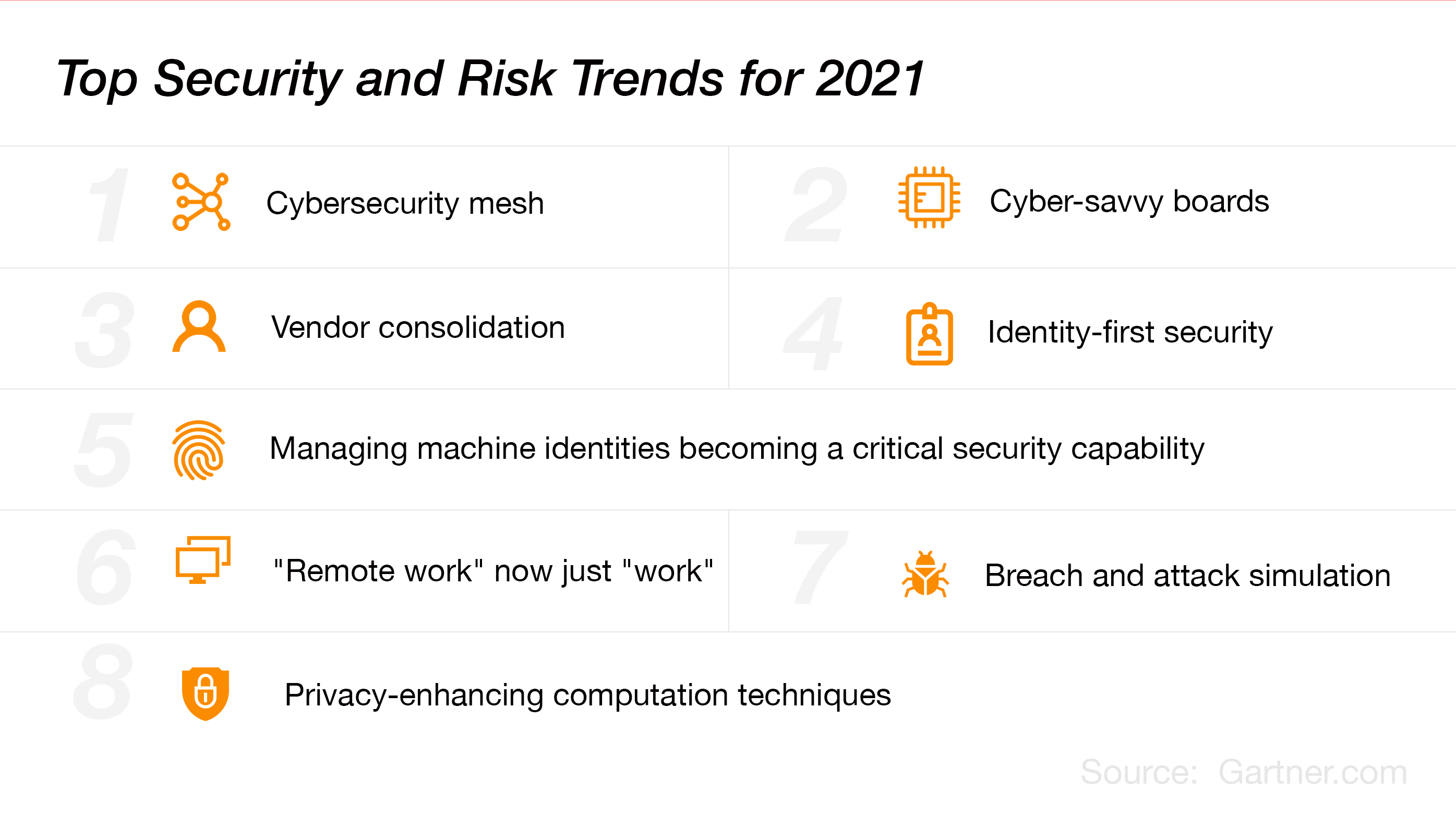
Since March 2020, attacks have become more intelligent. Classical security services like the Microsoft Defender are not bullet proof anymore (as stated by Gartner).
We get lots of requests on what to do. The first step, to quote Douglas Adams: "Don't Panic !"
Panic will only lead to immature solutions and risks to create even more open flanks for hackers.
I would like to develop an answer in 4 steps:
- What is intrusion and what are the reasons?
- Can we completely protect ATC infrastructure against intruders?
- What are the tools that ATC needs to react successfully against attacks?
- Do ATSEP have to do it themselves, outsource, or mix?
You cannot completely protect your infrastructure against attacks. But you can get very close. It is in fact a cat and mouse game of attackers finding new loopholes and defenders closing them. And for the case, that attacks success in bypassing the security systems, ATC needs subsequent breach & attack detection (and elimination).
We speak of attack vectors when we talk of the means, by which the intruder gets access. The attack surface is the area that is being attacked. Mary Shacklett published a nice article on TechTarget, for those who want to dive deeper.
Important to know: there are
- External entrance gates like email, the web, or the many APIs which connect external and internal systems (flight data, Radnet, MLAT etc). Solutions which protect these entrance gates are called Network security
- Internal entrance gates can be local installations like computers, servers, or a radar (which is a big computer too). We speak of endpoint security.
Attacks can only get in, when there are weak flanks.
We can divide them into
- Human weaknesses (human unthoughtfulness or lack of training, or malicious people inside the organization)
- Weaknesses in the IT architecture
And who are these hackers. There are two main groups:
- governmental hackers who try to influence other states, like the US elections in 2016
- criminal gangs who want to press ransom out of there victims (easily millions, when they paralyze a system like the America gas pipelines or a big company.
A third group are political activists who want a reach a political goal, independent of any official body. A small group consists of joyriders who attack for fun. This can be a costly hobby, especially for the parents when these attackers are minors.
2. Can we make the ATC infrastructure completely protected against intruders?
We cannot close these loopholes by a100%. But we can get very close and avoid damage.
We could hermetically seal off systems. Disconnect them from the outside world. However offline-subsystems are increasingly impossible in our data- and AI-driven world.
A major step into the right direction is to set up cryptographic public key infrastructures (PKI), where the keys are generated in a highly protected hardware security module (HSM). Public key infrastructures are procedures implemented across specific hardware and software which manage digital certificates and keys. These certificates and keys are used to encrypt data at rest, in use or in transit, so that no unauthorized person or system can read it. Everything within an organization should be protected. Even a firewall is powered by such a key. All your financial transactions are too.
An intruder who cannot access or read data is helpless1).
But these certificates and keys are used for more. Digital identities assign a certificate to a person, and the authenticity of that person is supervised by a certificate authority (which is a system, controlled by security experts). To make it really safe, digital identities should be verified by Qualified Trust Service Providers. These are external organizations, certified by governments, e.g., by the European Commission in compliance with the eIDAS regulation.
Also systems (like the computer of an employee or a radar) can be protected by such keys and certificates. Modern publications use the word "machines" to describe such systems, and "machine identity". The cartridge term "machine" embraces mobile devices, Internet of Things (IoT) devices including radars, Network appliances and routers, Web services and application servers, cloud instances, containers, microservices, clusters or smart algorithms. All those "machines" can get a specific cryptographic identity. So the tower will always know whether data is really coming from a radar / employee, or from a malicious agent.
When enforcing multifactor authentication (e.g. a password, an sms TAN combined with a digital identity or a biometric recognition system), hackers really have difficulties in breaking into a system. Let us not talk about simple password protected systems in ATC. Such a policy is simply grossly negligent.
3. What are the tools that ATC needs?
There are three layers of systems which are needed in ATC
- Tools that catch potential threats
- Tools for network-based threat detection.
Such tools are sophisticated email scanners, API Scanners or website scanners - Tools for endpoint-based threat detection.
Sometimes threats like trojans or viruses get through or they deviate the network-based protection, e.g. by an attacker who sticks his USB with malicious code into an internal computer. All endpoints should be connected to such detection systems
- Tools for network-based threat detection.
- Tools that analyze suspicious code
Such analytic systems push the code into a so-called sandbox and do an intense check. The engineers at VMRay.com published a nice video which explains how such a sandbox works. Around the sandbox there are lots of algorithms, external comparative data and AI, which tries to detect malicious code, without the code detecting that it is scanned. - Automated procedures (SOAR)
The most professional team cannot do anything if they have no automated support. There are too many concurrent potential threats entering and analysis periods per data package must be very short (imagine radar data arrives late...).
The solution to this are the platforms for Security Orchestration, Automation and Response. My colleague Alex Cosper published a nice article on these SOAR systems which is worth reading.
A SOAR solution is the result of three technologies working together, which are:
- Security Incident Response Platforms (SIRPs) - These platforms facilitate case/incident management and workflows as they collect data that becomes part of an incident knowledge base.
- Security Orchestration and Automation (SOA) - This technology involves integrations, play/process/workflow automation and playbook management.
- Threat Intelligence Platforms (TIPs) - This combination of platforms allows for TI aggregation, curation and distribution, TI visualization and sending alerts.
4. Do ATSEP have to do it themselves, outsource, or mix?
The NIST has published a nice list of pros and cons for either of these solutions.
Our standpoint is clear:
- you cannot win alone, so make use of Managed Security Service Providers (MSSP) who work remotely or in-residence in the organization.
- but you cannot delegate responsibility. And you need to have the intel inhouse, and accumulate knowledge and experience. So build up your ATSEP expert team in parallel. And develop your own security operations center SOC.
ATC can implement such a bipedal solution through a staged approach:
- First implement systems for system protection (cryptographic protection) and for threat defense. Hire an MSSP to get started in due time
- Develop your own ATSEP competencies in parallel to the point that you can provide the responsibility and ownership which passengers expect from you.
Gartner by the way highlighted cyber-savvy boards as one of the top 3 trends in cyber-defense.
SkyRadar can help you with our Breach, Attack and Defense Simulator for Cybersecurity in ATC.
1) Comment on the statement: "An intruder who cannot access or read data is helpless":
I discussed this simplified statement with the cryptography expert Martin Rupp. The statement is valid with respect to data privacy. The hacker cannot decrypt the data as long as he does not have the key. However he could over-encrypt the data a second time with a key, unknown to the owner of the data. That would enable him to ask for ransom money in exchange of turning data readable again. From that point of view, threat defense and analytics is very important.
About the Author
The author, Dr. Ulrich Scholten is cofounder of SkyRadar. He has been working on internet platforms since the early 2000s. Ulrich holds a PhD in information technology. He is author / editor of articles on cybersecurity with more than 30.000 monthly readers. His research is regularly published in highly rated journals and conference papers.
References and Further Reading
- Read more about Cybersecurity for ATSEP and AVSEC (2019-today), by Alex Cosper, Dawn Turner, Martin Rupp, Peter Smirnoff, Ulrich Scholten and Dennis Vasilev.
- More articles on Cryptography, Key Blocks and Key Management (2018 - today), by Martin Rupp
- Articles on the protection of critical platforms and strategic response (2017 - today), by Ulrich Scholten and Stefan Hansen
- Malware Analysis (2021) by VMRay
- Articles on Key Management and HSMs (2017 - today), by Peter Smirnoff
- Articles on Digital Signing, the eIDAS standard, cyber-security and ATSEP qualification (2016 - today), by Dawn M. Turner
- Gartner Top Security and Risk Trends for 2021 (April 2021)