Endpoint detection and response (EDR) provides continuous monitoring and analysis of endpoints, aiding incident response teams in efficiently managing threats and reducing overall response times in cybersecurity operations.
Introduction
At the time of writing, there is quite a lot of discussion among security software vendors over what is best around MDR, EDR and XDR when it comes to quickly identifying and removing threats from your endpoints. Managed Detection and response or “MDR” is a service that security providers provide to companies that lack the resources to help triage and handle threats detected in the environment. Endpoint detection and response is focused on the software side such as what is seen from companies such as SentinelOne & Cybereason among others. They offer security solutions that help secure the endpoints and provide a way to create playbooks where you can tell the program what to do if a threat is detected.
What is EDR?
Endpoint detection and response (EDR) is used to detect suspicious or malicious activity on endpoints such as laptops, desktops, and servers. Just like a security camera, this technology is always monitoring and actively reviewing what is occurring on the endpoint. It monitors running processes and records what is observed which can be played back later. While Anti-Virus traditionally relies on signatures and scheduled scans, EDR solutions are “always on” meaning they are continuously scanning and monitoring the endpoint for potential indicators of compromise.
How EDR Enhances Capabilities of Incident Response (IR) teams and reduces Total Time to Respond
Security teams are constantly overwhelmed with trying to stay ahead with the thousands of alerts and tickets they receive from traditional SIEMS. As leaders that manage security organizations and incident response, teams seek out ways to automate low level repeatable analysis work, and the concept of endpoint detection and response has caught the attention of these teams for the many areas it can help.
Key areas EDR streamlines incident response teams:
- Streamlined threat detection process with detailed forensic level details on chain of events in malicious activity.
- Near real time threat detection and alerting
- Detailed and enhanced reporting capability and quick triage over a large environment for additional infected machines.
- Ability to remotely isolate infected assets from the network for investigation and remediation
- Most EDR solutions use machine learning and behavior analytics to speed up detection of anomalies early in the kill chain prior to a breach occurring.
- Ability to create playbooks within the solutions to automatically triage and remediate detections and apply the findings across an enterprise
How Incident Response Teams Can Leverage this Technology in True Incident
Prior to the widespread adoption of EDR tools, incident response teams had to spend a significant amount of time manually gathering data from infected machines, working with server owners and other IT teams to collect evidence, and then manually analyzing it, which could take weeks or even months to get through.
As we have established, EDR solutions allow you to track everything in a single portal and group assets together that show similar signs of compromise. Endpoint detection and response tools also equip Incident response teams with the ability to immediately kill a malicious process and block it across an organization as soon as it is identified. As a result, reducing the ability for the malware or malicious activity from moving laterally across an organization. The capability to at scale, quickly investigate and respond to such incidents such as a ransomware situation, can save countless hours and downtime for any organization and team.
Additionally, incident response engagements would result in long, painstaking digital forensic investigations, which could add additional days or months to a breach recovery due to the time it takes to image devices. With EDR, it collects artifacts in a frequent manner, allowing the team to review forensic level data and quickly retrace the series of events that led to the initial breach on patient zero. These artifacts that are quickly discovered, can be leveraged to implement additional defenses across the security stack to mitigate future incidents.
Post-Incident
After an incident of any size or scale, most incident response teams monitor the impacted assets for a period to ensure they do not become reinfected. The root cause analysis that is provided to the threat monitoring team, can help focus where the threats could potentially reappear and with the new information, the team is better equipped with the knowledge and ability to eliminate and remediate similar incidents.
Once an incident is declared over, the EDR solution can give management peace of mind by ensuring that their teams are equipped long term to monitor and ensure that the newly cleaned or remediated systems stay secure and show no signs of potential backdoors that could have been left behind by the threat actors who were missed at the time of the incident While no solution is perfect, the key to success for any organization and incident response team is to automate where possible and ensure that you have the right level of data visibility to help reduce the time to respond to and mitigate a breach. While even EDR is not 100% fool proof, threat teams and IR teams can leverage these tools as threat hunting tools to stay ahead of threats that have not fully become known or had a chance to establish a foothold in the organization.
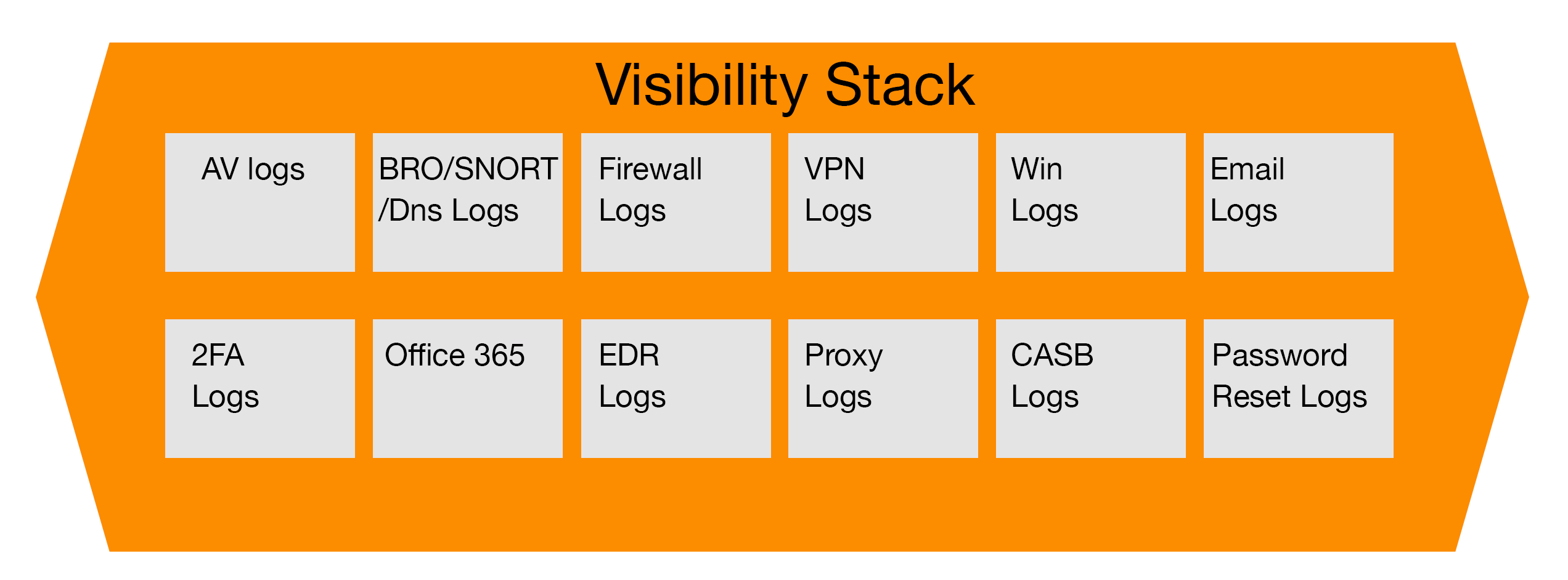
Endpoint detection and response tools have become a critical component of a proactive security organizations tool kit, and can relieve security operations and IT teams of the responsibility from having to ensure that all of their devices are properly configured to forward logs to a traditional SIEM.